Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
-
No low-effort posts. This is subjective and will largely be determined by the community member reports.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
view the rest of the comments
I've been using Tailscale for a few months now and this is my only complaint. On Android and macOS, the Tailscale client gets randomly killed. So it's an extra thing you have to manage.
It's almost annoying enough to make me want to host my services on the actual internet....... almost... but not yet.
I use plain wireguard on me phone, always on essentially with no issues. I wonder why tailscale app can't stay open.
Same, wireguard with the 'WG Tunnel" app, which adds conditional Auto-Connect. If not on home wifi, connect to the tunnel.
I just stay connected to wireguard even at home, only downside is the odd time I need to chromecast, it needs to be shut off.
I can stay connected, still works, but I don't think I need the extra hoops.
Can you add a split tunnel for just the Chromecast app (I presume that's how it works idk I don't use Chromecast) so that just that specific app always ignores your VPN?
I haven't tried it, but the app has the ability to select which app it tunnels.
When you make a new tunnel, it says "all applications" if you click on that you can select specific ones to include or exclude
Oh shit, you may have just solved my only issue with Symfonium
You don't need this with Tailscale since it uses a separate IP range for the tunnel.
Edit: Tailscale (and Wireguard) are peer-to-peer rather than client-server, so there's no harm leaving it connected all the time, and hitting the VPN IPs while at home will just go over your local network.
The one thing you probably wouldn't do at home is use an exit node, unless you want all your traffic to go through another node on the Tailnet.
I also have a different subnet for WG. Not sure I understand what you're saying...
If you have a separate subnet for it, then why do you only want it to be connected when you're not on home wifi? You can just leave it connected all the time since it won't interfere with accessing anything outside that subnet.
One of the main benefits of Wireguard (and Tailscale) is that it's peer-to-peer rather than client-server. You can use the VPN IPs at home too, and it'll add barely any overhead.
(leaving it connected is assuming you're not routing all your traffic through one of the peers)
My network is not publicly accessible. I can only access the internal services while connected to my VPN or when I'm physically at home. I connect to WG to use the local DNS (pihole) or to access the selfhosted stuff. I don't need to be connected while I'm at home... In a way, I am always using the home DNS.
Maybe I'm misunderstanding what you're saying...
He's saying that while there is no benefit to being connect to WG at home, there is also no downside so many people just stay connected all the time.
Yeah, this. Plus if you leave it connected, you can use the VPN IPs while at home instead of having to use a different IP when at home vs when out (or deal with split horizon DNS)
Oh, I get that, but it just doesn't make any sense to me to be physically next to the server, and connect to it via VPN...
My point is that since the VPN uses a different subnet, it's fine to keep it connected even at home. It'll only use the VPN if you access the server's VPN IP, not its regular IP.
In any case, Tailscale and Wireguard are peer-to-peer, so the connection over the VPN is still directly to the server and there's no real disadvantage of using the VPN IP on your local network.
Right, but I have wireguard on my opnsense. So when I want to reach https://jellyfin.example.com/ , if I am at home, it goes phone -> DNS -> proxy -> jellyfin (on the same network). If I am connected to the VPN, it goes from phone -> internet -> opnsense public ip -> wireguard subnet -> local subnet -> DNS -> proxy -> jellyfin. I see some unneeded extra steps here... Am I wrong?
Oh yeah, there'll be some overhead if you're running Wireguard on a router. Hitting your router's public IP won't go out to the internet though - the router will recognize that it's its IP.
It's common to run Wireguard on every computer/phone/tablet/etc where possible rather than just on the router, since this takes advantage of its peer-to-peer nature. For home use, that's how it was originally designed to be used. Tailscale makes it a lot easier to configure it this way though - it's a bit of work for vanilla Wireguard. Tailscale does support "subnet routers" if you have any devices that you want to access over the VPN that can't run Tailscale.
I don't think I've ever encountered what you say... I use WG it to access a network, not a device. I have a few dozen devices, physical and virtual, why should I set up wg on all of them? Tailscale, maybe, it's a different story, but I prefer to "self host" and not rely on a 3rd party provider. Wireguard was relatively easy to set up too, a few years ago... and in the meantime, if I need to add a new client, it's a two minute job.
I suspect that it goes down and stays down whenever there is an app update, but I haven't confirmed it yet.
Does the plain wireguard app stay up during updates?
Android wireguard all hasn't been updated in 18mo. Its extremely simple with a small code base. There basically isn't anything to update. It uses wireguard kernel module which is itself is only like 700 lines of code. It so simple that it basically became stable very quickly and there is nothing left of update right now.
https://git.zx2c4.com/wireguard-android/about/
I personally get the from obtainium to bypass play store
If you make Tailscale your VPN in Android it will never be killed. Mileage may vary depending on flavor of Android. I've used this on stock Pixel and GrapheneOS.
Under Settings > Network and internet > VPN
Tap the Cog icon next to Tailscale and select Always-on VPN.
Holy moly, I did not know this existed! Thanks! Just turned this on!
Look up your phone on dontkillmyapp.com and make sure tailscale is excluded from battery and network "optimization".
Yeah my wife and I are both on Android, and I haven't been able to figure out why it does that.
The Android client is open-source so maybe someone could figure it out. https://github.com/tailscale/tailscale-android
It loses its foreground notification I've found that kills it for me
collapsed inline media
collapsed inline media
collapsed inline media
If I disconnect/reconnect the notification comes back, and I've found something even more weird on my device (A Xiaomi with its infamous OOM / background app killer....) is Tailscale still actually works fine most of the time without the foreground notification. I'm hazarding a 70% of the time for me?
A lot of us a while back found v1.5.2 fugged around with the persistent notification going RIP
https://github.com/tailscale/tailscale/issues/10104
Oh the Quick Toggle has never, ever worked correctly. I hoped they fixed it after the UI refresh update but unfortunately not yet.
What device/ROM are you using?
It's been very iffy for me on and off from Miui > HyperHyperOS, but just checking now?
Works fine
collapsed inline media
collapsed inline media
Like I say, the foreground notification seemed to be the lifeline to some of us using it and keeping it alive, even after IIRC some more restrictions came in with future versions of Android (forgive me, I'm very lazy these days and just skim Mishaal's TG feed 😇)?
e: also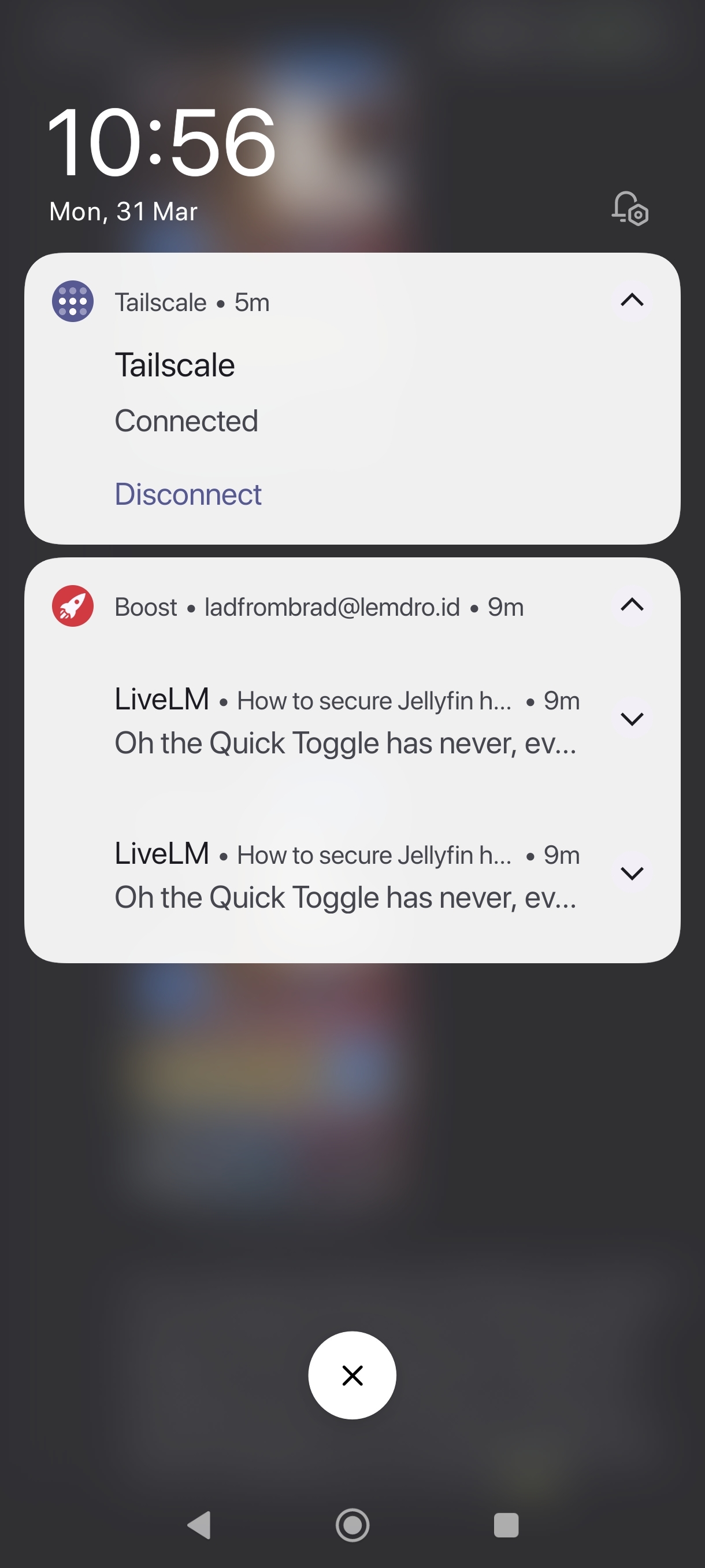
collapsed inline media
For me it's always been busted both on AOSP and Miui/HyperOS...
Huh. The nearest I have to an actual "AOSP" device is my King Kong Cubot phone that has probably the cleanest version of "stock Android" I've ever seen, and I'm going to presume you mean like a Google Pixel / Graphene etc?
Tailscale and the QS tile / notification was solid on that Cubot but to be honest, I've barely turned it on these days and is now one of those drawer phones.
Miui / HyperHyperOS though is a different kettle of fish and exempting Tailscale from its App lel Killer does seem to work. 70-80%ish.....
But there is something that just fuggs up and turn it off/on like most thingys I own 🙈
Works great and has been for some time on my P7P.
Ensure you've allowed background usage and turn off manage app if unused.
Keep the notification on and allow notifications.
collapsed inline media
collapsed inline media
Oh the Quick Toggle has never, ever worked correctly. I hoped they fixed it after the UI refresh update but unfortunately not yet.
Try WG Tunnel instead. It will reconnect on loss, but you lose the Tailscale features (no big deal with dynamic DNS)
Maybe headscale will do better?
Headscale is a replacement for the coordination servers, which are only used to distribute configs and help nodes find each other. It won't change client-side behaviour.